A few days ago, we commented in this post about the different types of user accounts possible in Windows and how (a responsible administrator) should have tools and the ability to protect the system and users from outsiders and themselves;)
Let's now see the possible users we have in a system GNU / Linux:
* root : is the user super powers or administrator, let's say. The root user has full permissions on directories and files (no matter who owns them), can install and uninstall software, perform modifications about the whole system, manage user accounts, etc. You have the control and responsibility that the system or the pc works correctly.
* special users (or also system accounts): these accounts, which are generally created when the distribution is installed, do not have a password as they are created in order to have some access privileges. root to carry out specific tasks, but not to log into the system with them.
* common users: these are normal user accounts, for you and me. When creating a new common user, our own working directory will be created (in / home / our_user). Obviously we have privileges over our work environment and our files, to which we can modify them as much as we want.
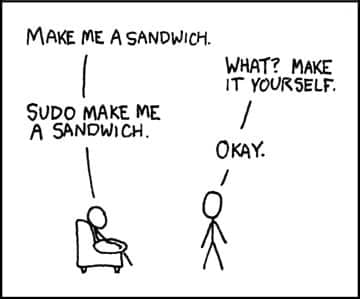
And if now I, common user from my distro, I need to install something: what should I do? I can choose to ask the system administrator to install it for me or ... use the command su O well sudo.
It is very clearly explained on Wikipedia:
The program su is a utility for Unix-like operating systems that Allows you to use another user's shell without logging out. It is commonly used for get root permissions for administrative operations, without having to exit and re-enter the system. Some desktop environments, including GNOME and KDE, have programs that graphically ask for a password before allowing the user to execute a command that would usually require such access.
Name su comes from the English ssubstitute uto be (Change user). There are also those who make it derive from superuto be (super-user, that is, the root user) since commonly used to take on the role of system administrator.
This means that, from a console terminal or from the graphical interface in some cases, some action could be executed as a user root. For this, I must enter the password of said user and, if it is correct, continue.
Even if we don't know the user's password root (and this, in my opinion, is the perfectly correct thing to do) we have another option to install what we should install: the command sudo.
The command called sudo eexecute a command as another user, respecting a series of restrictions on which users can execute which commands on behalf of which other users (usually specified in the file / Etc / sudoers). Unlike su, sudo prompts users for their own password instead of the required user; this to allow the delegation of specific commands to specific users on specific machines without having to share passwords, at the same time reducing the risk of leaving terminals unattended.
We could say then that, if we are responsible users of our system and we belong to the group sweats, We should not have problems to handle ourselves with peace of mind (I mean an average user, the account that we could create on the pc for our father / mother / cousin / grandfather / boyfriend / girlfriend ...) or, if we are the root user, with extreme care.
Reading around I found that it is recommended In general try not to log in and constantly operate as the root user, but create a normal user account and, if necessary, use su. This is done because the errors that might be made in the normal or average use of the pc will be more manageable in a common user environment and not at the level of the whole system, right?
And now that I think about it ... security hole or not ... after all, users on both operating systems are handled in very similar ways. The administrator or root in GNU / Linux has greater control, with respect to Windows, in who will be the ones who carry out administrative tasks and make changes to the system. From this it can be seen that the confidentiality and complexity of the administrator password is of the utmost importance, which, if it were fooled or discovered, would jeopardize stability (I have said stability and not security, which was already violated if the root password is discovered) of the entire system.
In conclusion, I am left with what was stated on the previous occasion: we will have stable systems or machines as long as users and especially administrators are responsible, otherwise ... simply, No..
Greetings dear, I await your opinions :)
in that it is a point for linux, since an individual X can arrive and even if he discovers the password of the normal user, it will cost him an egg to uncover the root one!
but in windows you discover the administrator password (which is not so difficult) and boom! you can now uninstall programs !! XD
greetings !! and good article! ;)
I think, as osuka says, discovering the root one takes time.
But come on, something that I liked and I quote from the post: «... we will have stable systems or machines as long as the users and especially the administrators are responsible ...» this for me is the key to the success of security. I have not been a direct user of Windows for years (direct user because I do not have it installed at home, I only use it at the University for some payment programs that are used there), but when it was, very few times huh had problems with viruses and others. So, I think the key is in the training of users and above all, in those who work installing networks and equipment for companies / banks / state departments. Since a human failure can generate a computer failure. I mean, a bit superficial, then tmb has to see if the system is good or not, but it is another issue, if the user is capable of being subtle, it should be more complicated (not impossible) than normal, to enter a system.
See you
Excellent work with the article N @ ty.
I wonder: Is a Linux user logging in as root as vulnerable as a windows user? and backwards
Is a Windows user logging in as limited as safe as a Linux user?
Aaa ... I translate what he said? ... I don't understandoo ... don't be elitist !!!
@ Thank you all for the comments, after all it was quite similar… much safer, it's true, but similar….
YOUR entry is SUPER interesting ...
It is logical that Linux is too secure, due to its security algorithms and the management of the Administrator. This prevents any user from wreaking havoc on our system, and in turn protects us from malicious intrusions of malicious programs, or also known as viruses ...
It is so logical that it should be so, that many times I do not understand how security is too easy in Windows.
sudo rm esty
sudo rm esty = I am a friend of god and I delete esty
erase esty ???… haha… you'll see, I found something very interesting to get even for Saturday's post. : D
@esty: rm is like the DOS delete command, that is, it deletes something. In this case, delete esty
The command "sudo rm -rf /" recursively deletes the folders without asking (for the -rf) what is inside / (which is the root directory, which contains all the media connected to the computer, including, but not limited to all hard drives, pen drives, memory readers, etc.
So if it ever occurs to you to switch to linux and a troll tells you to put that on, don't do it;)
@esty: This is a declaration of war!