You know how to update BIOS from your PC? With vulnerabilities such as Specter, Meltdown, and all its variants and other security holes detected in the hardware, especially in the CPUs, you have surely read many times that many of them are solved by knowing how to update the BIOS or UEFI of your computer. , since an update or patch is needed for the microcode used by the CPU and thus alter the way the CPU Control Unit operates so that it is not vulnerable to said threats.
In addition to vulnerabilities, firmware can be updated for many other causes, such as a malfunction of a hardware device, constant errors in the software in an inexplicable way, updates to add some functionalities, etc. But as I said, in recent months we have heard this term too many times due to security problems that are quite critical in some cases and that had to do with the way in which modern microprocessors handle some jumps, cache, FPU and speculative execution, although in other cases they have been detected in other parts of the system such as chipsets or certain security processors integrated in these platforms ...
What is firmware?

We are all quite clear about what hardware (physical and palpable part of a computer, that is, electronics) and software (that logical part that cannot be touched: programs) are. But between the hardware and the software, or rather, between the hardware and the kernel of the operating system there is something else: the firmware. Firmware is present in all devices and parts of a computer, from the mouse, the optical drive, to the GPU and CPU that operate with a microcode.
But what is it? Well you can say that is code, that is to say, software and therefore a logical component but this time it is unalterable. It operates at a low level, and directly controls the functionalities of electronic circuits. This firmware, with the help of the controllers or drivers, allows that when the kernel of the operating system commands the hardware to perform a task, it will execute it. This program or code has been recorded by the device manufacturer in a memory that is usually flash, or some type of ROM such as EEPROM.
But one of the firmware that interests us most in this article is the BIOS or UEFI of a system, since it is a very important firmware that has various functions during the start-up and operation of the equipment. For example, this code is responsible for activating the machine during startup, detecting hard drives or media where there is an operating system available, performing some checks interfering with other firmware of the components and peripherals, and giving control to the kernel when the system starts to start ...
Why does updating it affect the CPU?
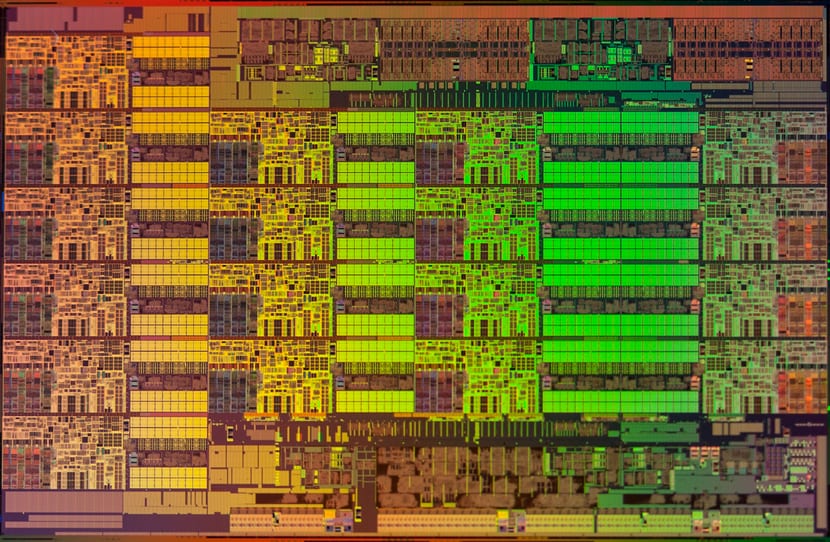
... and this has to do with the CPU, well enough. Turns out CPUs have a control unit, This control unit is a circuitry that is responsible for controlling the rest of the parts of the microprocessor or CPU, such as decoding the instructions and making the data with the operands go to the appropriate registers and then activating some functional unit such as an ALU or FPU and that it performs some operation on the data depending on the type of instruction that is being executed. These instructions in turn come from the program or software code that is being processed at that time, since as you should know, programs are made up of a series of sequential instructions.
As you can imagine, this control unit operates in a way that the manufacturer or designer created it. In some specific cases the control unit may be wired, that is, they are usually quite fast but not very flexible, since they are implemented directly with a very specific circuitry. On the other hand, there are also programmable ones, that is, a somewhat more "open" circuitry that can operate in one way or another according to a microcode or firmware. It follows therefore that if we change the firmware or microcode we can make the control unit and therefore the CPU can operate differently or correct some bugs or vulnerabilities.
I do not want to get too technical, I want this article to reach as many people as possible and that everything I want to say is easily understood ... And in many machines it turns out that this code is usually integrated into the BIOS or UEFI , although sometimes the microcode can be updated through the kernel during each boot, saving the update or patch in volatile memory, that is, in RAM, avoiding having to alter the BIOS / UEFI.
How to update BIOS / UEFI from Linux?

To update BIOS / UEFI from Linux or microcode, let's break down both procedures.
Before performing a microcode update it is very important that you have updated BIOS / UEFI firmwareas otherwise it might not work. So check the website of your firmwre provider like Phoenix, Award, etc., or the technical support website of your motherboard model, which usually have packages to update these systems.
Updating the BIOS / UEFI is something delicate as you can see in the last section on risks. That is why I advise you not to do it if you are not sure what you are doing and if you want to update or you need it, but you do not have enough knowledge, always consult a professional. In addition, I would recommend you take a look at projects such as fwupd, BIOSDisck, Flashrom, etc., which are very practical tools that will help us in the process.
One of the ones I like the most is flashrom, It is a package that gives us a tool that allows to identify, read, write, verify, and erase flash chips. This not only serves to flash a BIOS / UEFI / CoreBoot, it also serves to modify other flash memories of network cards, GPUs, etc., in other devices with modifiable firmware. It also supports various operating systems and a multitude of gears and models of devices and boards.
- Install the flashrom package in your distribution using the package manager that you normally use, since it is a tool that is among the repositories of the most important distributions.
- Use root or sudo, since to use it you need privileges to be something delicate.
- Identify the firmware which we use by simply executing the command:
flashrom
- I recommend that you do a backup your current ROM, in case you find that the new update does not work and you want to go back. For it:
flashrom -r copia_seguridad.bin
- Yes already we have the new ROM which we have downloaded from a RELIABLE source, we can use the following command to flash, for example if our new update is called uefi-sm.bin:
flashrom -wv uefi-sm.bin
For more information consult the manual with man flash rom.
Update microcode:
To update the microcode of our CPU, without touching the BIOS / UEFI, that is, with a simple modification in the Linux kernel, you can choose to install the necessary packages for your CPU. For example, if you have a modern AMD CPU, it is normal that install the package called amd64-microcode, and for an Intel the package intel-microcode (if you use openSUSE, SUSE, RHEL, CentOS, etc., the package is called microcode_ctl, and for Arch intel-ucode or amd-ucode ...) that you can find on trusted websites ... (that if it is an x86 machine, if it is ARM or different, go to the manufacturer's website). Insisto a pesar de parecer un pesado, no descargues este tipo de paquetes desde fuentes desconocidas, es muy importante. Bien, ahora que ya lo tenemos descargado e instalado, puede que el procedimiento sea diferente en cada distribución y que implique activar algunos paquetes o actualizaciones restringidos como los propietarios…
With those packages installed and the system settings referencing updates well configured, lown security updates that installs the operating system will already include this type of microcode patches if some serious vulnerability has been detected, such as Specter, Meltdown, etc.
If you want, you can get microcode information from your distro using:
dmesg | grep microcode
And with that we will obtain microcode detailsIn fact, if we have executed this command before installing the packages that I mentioned before (after installing it is necessary to restart) and afterwards, we will see that it shows us changes if there was an available update that has been installed.
Sometimes AMD, Intel, and other CPU manufacturers or designers provide tarballs with binary blobs to update microcode or firmware. If you have downloaded one of these packages from a reliable place, follow the instructions provided by the distributor or consult the README files.
Dangers and tips before updating the BIOS

A firmware or microcode update of the CPU means in most cases updating closed codes provided by the CPU providers that we have, closed kernel drivers (binary blobs), etc. I want to make this clear, since its content and way of operating is unknown and it seems logical that you should know. In principle, if you do not use free hardware, you have no choice but to trust the manufacturer or designer of your CPU or motherboard, but yes, never ever download microcode or firmware from unofficial websites, since it is something very delicate.
In fact not only it's delicate for security reasons, since you could also make the equipment totally unusable. Even if you have downloaded the firmware from a trusted website, something may go wrong during the process, such as a power outage and that leaves the update installation and the firmware completely corrupt, which means that you may already be thinking in spending money to buy a new motherboard.
This is what is known by the term brick in hardware slang, that is, leave your hardware like a brick, without any kind of utility. With this I want to tell you to be cautious and that we are not responsible for what may happen if you decide to update a firmware or flash the BIOS / EFI. But beware, this does not always involve risks, as I have told you before, you do not always need to "touch" the BIOS / EFI, there are also updates that are only at the OS level and do not involve those risks ...
I hope this tutorial has been useful, any questions or suggestions, do not forget to leave your comments...
hello good morning I wanted to install xubuntu 14 on my notebook, and download the files, install them but when it asks to restart from the usb key, I enter the bios and I cannot find the flash memory in the boot menu, someone can help me, From already thank you very much.
Hello friends:
The article seems to me, excellent although "dangerous" for those of us who are more novices and fearful.
I've been missing a good article for a long time that makes us understand how a multifunction printer system like mine (Canon MG 7150) works over Wifi.
With Linux, I have never made it fully work. I have managed to make the printer connected by USB work, but never the scanner, neither by Wi-Fi nor by cable.
That is why today I bring up the subject and at the same time I thank you for providing us with articles of such quality as the present one; but at the same time, I would like someone who knows how to do it, make it easier for us to make the aforementioned system work.
Thanks and kind regards
First look in the BIOS if there is the MULTIBOOT option (where you have to activate it), if not, it exists, to boot with a USB generally when you turn on the PC you have to hold down the F8 key for a while (in other PCs it is usually F12) and there the boot menu jumps showing the options: hard disk, CD, USB. In case of having UEFI, the USB must be generated with the UEFI option otherwise it is not recognized