2020 it is not being a good year in terms of computer security. David told them the other day the sale of Zoom accounts. And it seems that this time it was the turn of GitHub, Microsoft's hosting and version control service. It was reported that many of its users are being the victims of a phishing campaign designed specifically to collect and steal their credentials through apocryphal pages that mimic the GitHub login page.
GitHub accounts are stolen. A real danger for developers and users
Immediately after taking control of an account, heThe attackers proceed to download the contents of the private repositories without delay, emphasizing those who They are the property of the organization's accounts and other collaborators.
According to GitHub's Security Incident Response Team (SIRT), these are the risks
If the attacker successfully steals the credentials of the GitHub user account, they can quickly create personal GitHub access tokens or authorize OAuth applications on the account to preserve access in case the user changes their password.
According to the SIRT, this phishing campaign called Sawfish, it can affect all active GitHub accounts.
The main tool to access accounts is email. The messages use various tricks to get recipients to click on the malicious link included in the text: some say unauthorized activity was detected, while others mention changes to repositories or to the target user's account settings.
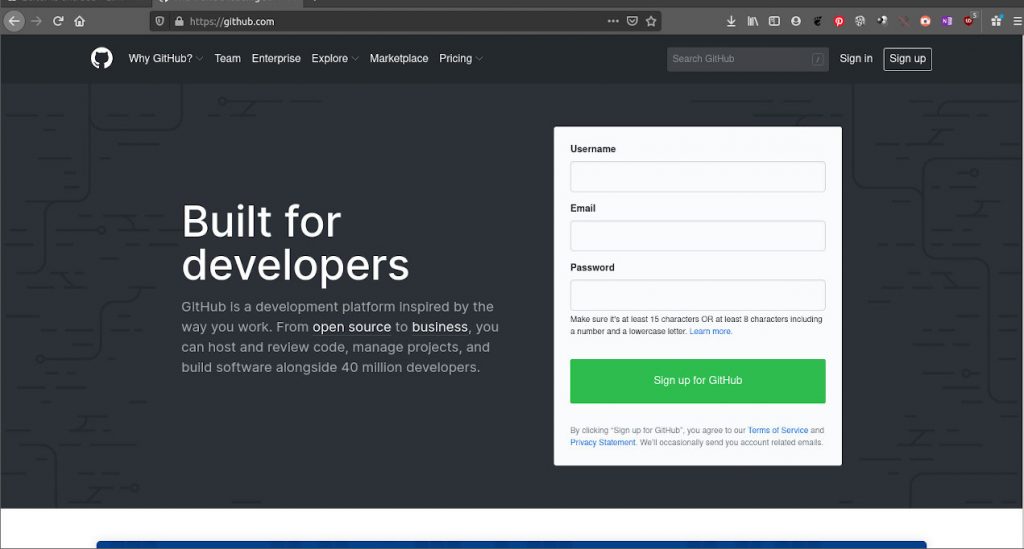
Users who fall for the deception and click to check their account activity They are then redirected to a fake GitHub login page that collects their credentials and sends them to servers controlled by the attacker.
The fake page used by the attackers you will also get the two-step authentication codes in real time of victims if they are using a time-based one-time password (TOTP) mobile app.
For the SIRT so far, accounts protected by hardware-based security keys are not vulnerable to this attack.
This is how the attack works
As far as is known, the preferred victims of this phishing campaign are currently active GitHub users working for tech companies in various countries and they do so using email addresses that are publicly known.
To send phishing emails se use legitimate domains, either using previously compromised email servers or with the help of stolen API credentials from legitimate bulk email service providers.
The attackers tThey also make use of URL shortening services designed to hide the URLs of the landing pages. They even chain multiple URL shortening services together to make detection even more difficult. Additionally, the use of PHP-based redirects from compromised sites was detected.
Some ways to defend yourself from attack
According to the recommendations of those responsible for security, if you have a GitHub account, you should do the following:
- Change Password
- Reset the recovery codes in two steps.
- Review personal access tokens.
- Switch to hardware or WebAuthn authentication.
- Use a browser-based password manager. These provide a degree of protection against pishing as they will realize that it is not a previously visited link.
And of course, one that never fails. Never click on a link sent to you by email. Write the address manually or have it in bookmarks.
Anyway, it is surprising news. We are not talking about a social network but a site that according to its own description is:
a collaborative software development platform to host projects using the Git version control system. The code is stored publicly, although it can also be done privately ...
In other words, its users are the people who create the applications that we use and therefore who have to add security features. It's kind of like stealing from the Police Department.