The folks at Microsoft have not even bothered to remove the Stickykeys trick, thanks to which we will be able to crack a Windows password using Linux
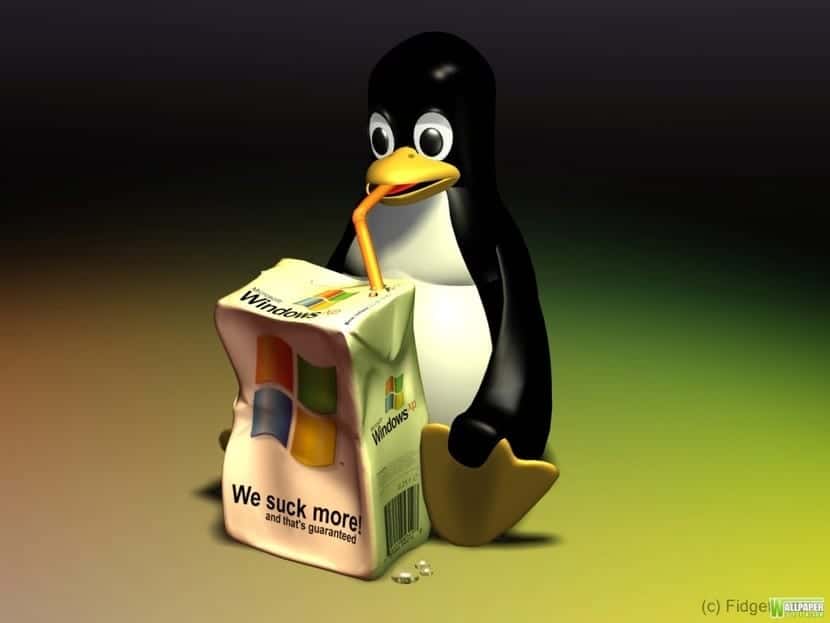
You surely know that Windows is known for its countless security bugs, which appear very often and countless times Microsoft let's say that it forgets to correct them, even the simplest ones.
So much so, that anyone with a cobasic knowledge of Linux operating systems, It is capable of violating a Windows password and entering with administrator privileges. The simplest method that exists is the Stickykeys trick, which Microsoft has gone beyond correcting.
This tutorial is designed to be used on your personal computer, for example on that old computer that you have at home and you do not remember the password, therefore we are not responsible for misuse given to it.
Tutorial to get passwords to access Windows using Linux
- Access the desired computer with Linux, you can use a dual-boot installed operating system or a Live CD.
- Search with the file manager of your favorite Linux distribution for the following file, which is in C: /Windows/system32/sethc.exe and the file C: /Windows/system32/cmd.exe
- Make a copy of cmd.exe to your desktop Linux and rename it to sethc.exe.
- Copy the file back to system32 and replace the old file with the new one.
- Start the Microsoft operating system and press the shift key more than 5 times, if you have done it correctly, a window will open. MS-DOS.
- Type the following command to add user:
net user Linux /add
- Then type this command to put it in the administrators group:
net localgroup Administradores Linux /add
- Notice that the Linux user has appeared on the home screen and has access to everything.
This is curious since we are in Windows 10 and they have not been able to repair the error, which I find it somewhat regrettable because anyone with a little skill can get into a Windows computer, just by copying and pasting a couple of files. Remember that we are going to make more tutorials in Linux Adictos, like for example this one in which we learned to install Google Chrome
You have discovered gunpowder! That makes you worthy of the title of Tecnicoless.
The article is more to denounce the alarming lack of security of Microsoft systems, which are not even capable of eliminating this simple trick.
Actually, he wanted to play the "devil's advocate" role: he believed that this company was going to do well with the new version. But the truth is evident and undeniable. There is no easy answer to such an obvious failure and it should be easy to correct. Thank you for your response, we are always here to order.
Interesting for when an acquaintance forgets the password. I'll keep it in mind.
I did not know very good
This is already older ...
The thing is, they haven't changed it
Does it work for Windows 10?
CHECKED,
here the video with my tests on a VirtualBox machine:
https://www.youtube.com/watch?v=5HI1uKHy0qY
It is a pity that Microsoft is not careful in this regard. My friend like and thank you.
regards
And what do you want a distro for?… It is enough to start safely, it allows you to use the administrator account without a password, once inside you can change the password of any user
and what password has been violated? Physical access to a computer implies being able to access certain "tricks" to enter the system, you could also have changed the password of the administrator user or another user ...
It can also be done as you say.
regards
We use it with the hard drives of barcenas, since in the pp we use windows xp and windows millenium
With physical access to a computer you can always do many things :-P In most Linux installations you can access as root by editing grub. Sure, it's also possible to secure it with a little extra setup.
If with full access to a computer it is more difficult to protect it, you could still remove the Hard Drive and if it is not encrypted ready, or a live CD / USB, be it Linux or Win. Perhaps it is a more discreet way to enter, and it is very useful when there is support and they forget the passwords.
The last paragraph seems stupid to me, because to do what the tutorial describes, he had access to the "victim" machine, anyone "with a little knowledge" as described in the article can do the same against linux, a Linux live, a chroot to any linux and voila you already have root access ..
Of course always talking about partitions that are not encrypted ..
Because they make such a fuss, especially the "wise men", it is a good "trick" for people who do not have enough experience in managing systems to regain access to the pc ... period. Alla the "wise men" who talk about encrypted partitions, remove the hard drive, blah blah blah blah, it's true! the password has not been violated, only the pc was accessed. which could not. I appreciate the publication because it served me. There is another trick using the windows 10 installation disk using the command utilman.ex and cmd ... procedure which if it allows you to violate the windows password
I think you have mental retardation. it is not a microsoft or system error.
You are not "violating" the system since the windows system at the time you do "the hack" is not running.
The day you do it with the windows started and from a user without privileges, you come to fart with a high appearance
apologize to humanity and hopefully you get penile cancer
Nice story, but it is not true, Windows is not compromised because it is not running. On the other hand, and using the same method, I have entered a Linux machine just by adding a 1 at startup. I become root and can change whatever I want.
There is no reason to be alarmed, even the most secure systems have a back door in case the user is so stupid to lose their own keys.
Can't, Windows 10 partition prevents new file from being written to location.
Excellent tested on windows 10 with ubuntu 14.04 (old version I had on hand). I had to mount the NTFS partition with a command and then to do the tutorial !!!! It works perfectly.
My case was that I did not have permissions to access hdd
Opening terminal
Entering following command
Sudo chmod 666 / dev / sda »drive num»
Example:
sudo chmod 666 / dev / sda2
After entering that the file manager will have vision and control of modification as well as terminal