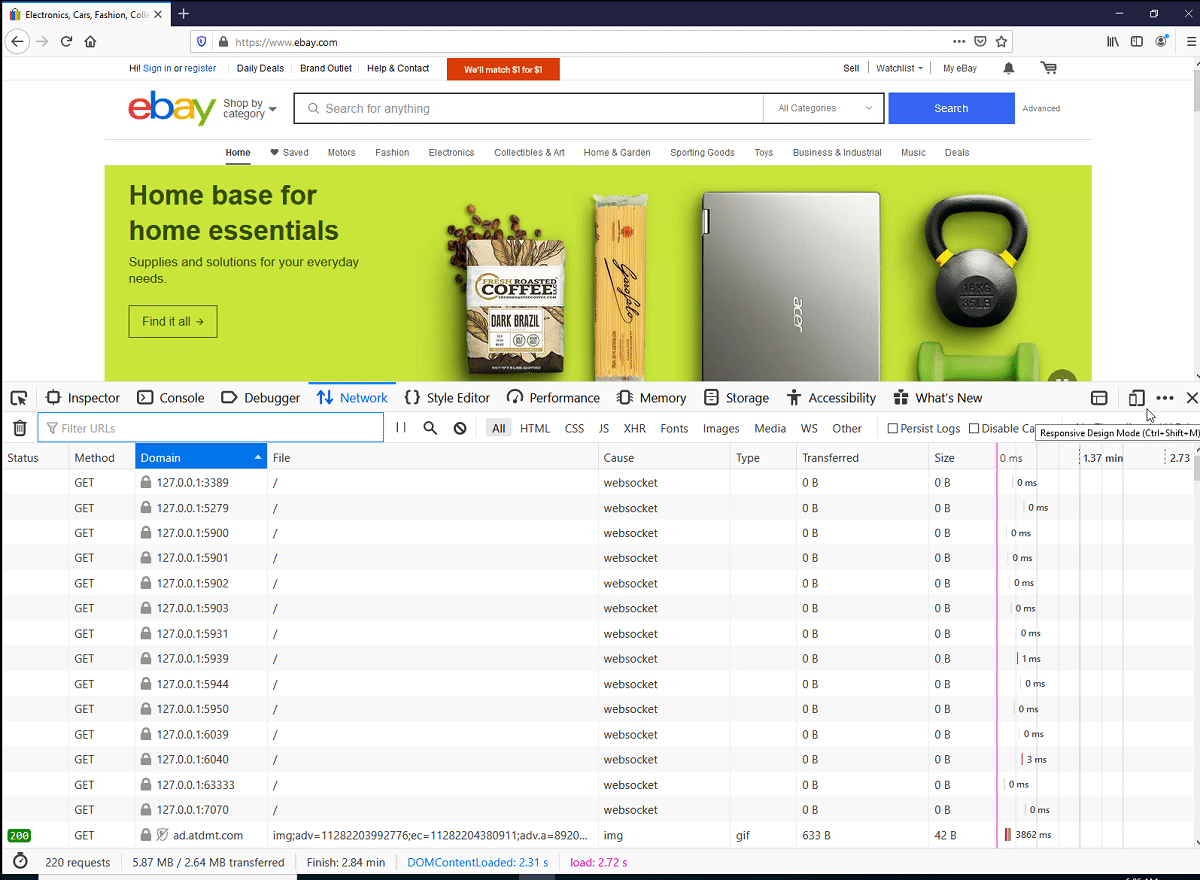
Recently, information was released about certain websites performing local host port scans against visitors, this is "presumed" as part of fingerprint and user tracking or bot detection.
Within those websites, only to mention one of the most popular that perform local port scanning is the eBay.com site.
Furthermore, it turned out that this practice is not limited to eBay and many other sites (Citibank, TD Bank, Sky, Gum Tree, WePay, etc.) use port scannings from the user's local system when opening its pages, using the code to detect attempted access to hacked computers, provided by ThreatMetrix.
In eBay's case, 14 network ports were verified associated with remote access servers such as VNC, TeamViewer, Anyplace Control, Aeroadmin, Ammy Admin, and RDP.
Most likely, the verification will be carried out to determine if there are signs of malware affected by the system to avoid fraudulent purchases using botnets. Scanning can also be used to obtain data for indirect user identification.
Before this uBlock Origin developer decided to take action in the matterto and in EasyPrivacy added rules to block standard scripts that scan network ports on the local user's system.
For scanning, a technique is used based on an attempt to establish connections to various network ports of the host 127.0.0.1 (localhost) via WebSocket.
Port scanning is a confrontational technique often used by pentesters or hackers to scan machines with an Internet connection and determine which applications or services are listening on the network, usually so that specific attacks can be carried out. It is common for security software to detect active port scans and mark it as possible abuse.
Whether you have an open network port is indirectly determined by differences in error processing when connecting to active and unused network ports.
WebSocket allows sending only HTTP requests, but a similar request for an idle network port fails immediately and for the active port only after a while it takes an attempt to negotiate a connection. Also, in the case of an inactive port, WebSocket generates a code connection error (ERR_CONNECTION_REFUSED), and in the case of an active port, a connection negotiation error code.
When configuring a web socket, specify a destination host and port, which does not have to be the same domain the script is served from.
To do a port scan, the script only has to specify a private IP address (such as localhost) and the port you want to scan.
A port scan can provide information to a website about what software you are running. Many ports have a well-defined set of services that use them, so a list of open ports gives a pretty good view of running applications.
For example, Steam (a gaming store and platform) is known to run on port 27036, so a scanner seeing that port open could be reasonably confident that the user also had steam open while visiting the website. .
In addition to port scanning, WebSockets can also be used to attack web developer systems that run WebSocket drivers for React applications on the local system.
An external site can iterate through network ports, determine the presence of such a controller, and connect to it.
Between introspection for error messages and timing attacks, a site can get a pretty good idea of whether a certain port is open.
If the developer makes a mistake, the attacker will be able to get the content of the debug data, which may include fragmentary confidential information.
If you want to know more about it, you can refer to the following post.
Source: https://nullsweep.com/
Could you indicate how to activate this function, or is it activated by default?
Thank you, greetings.
Let's say that it comes by default because if you have not configured uBlock it will update itself just like its filter lists. But if you want to make sure you just have to update the EasyPrivacy list. Go to the plugin preferences, then 'Filter List', search for EasyPrivacy, click on the clock, and finally on the 'Update now' button.