After almost four years of development the release of the new version of «Qubes 4.1» was announced which is an operating system focused on desktop security through isolation based on the Xen hypervisor. Qubes OS is a completely free and open source operating system.
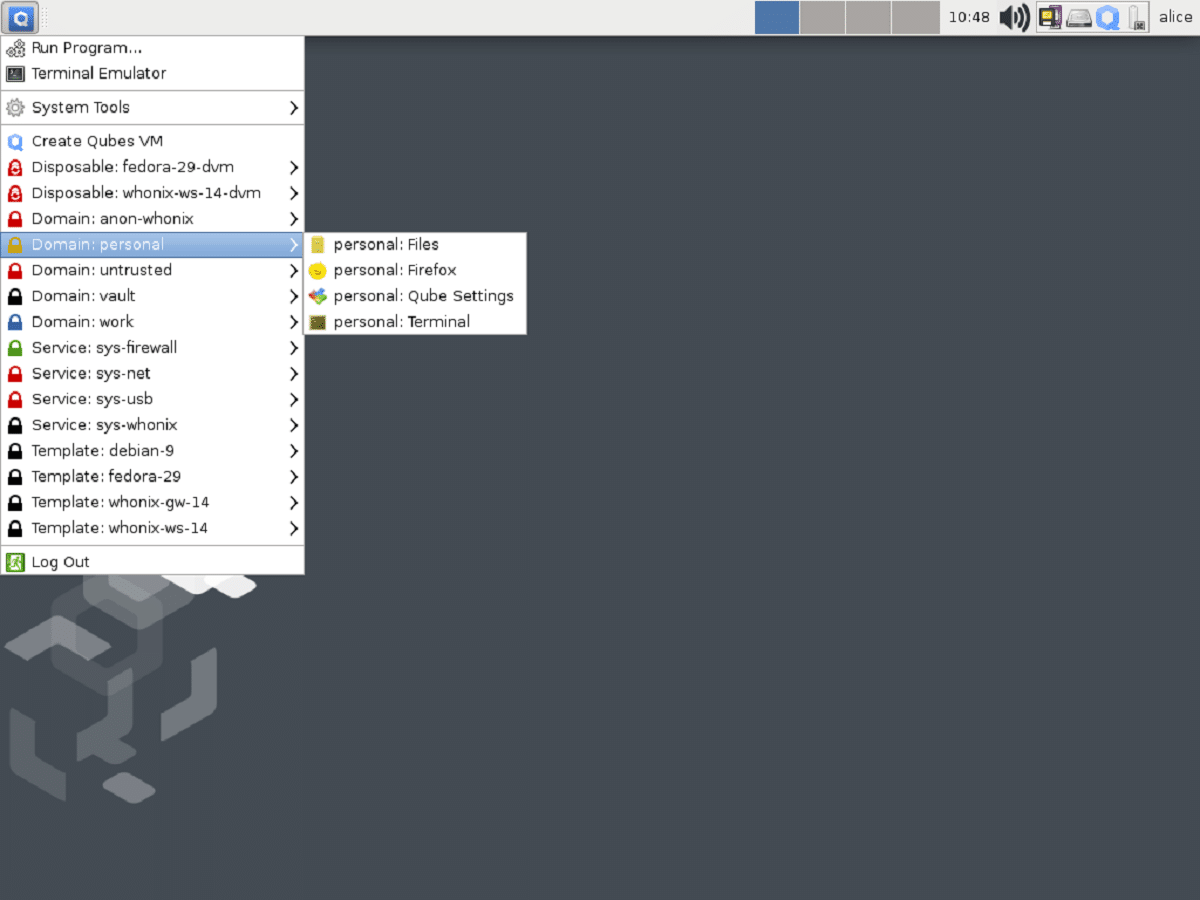
Qubes implements the idea of using a hypervisor for strict application isolation and the components of the operating system and in which the applications are divided into classes according to the importance of the data that is processed and the tasks that are solved.
Fedora and Debian can be used as a basis for building virtual environments, and the community also supports templates for Ubuntu, Gentoo, and Arch Linux, and it is possible to organize access to applications in a Windows virtual machine, as well as create Whonix-based virtual machines to provide anonymous access through Tor.
What's new in Qubes 4.1
In this new version that is presented, the experimental support for Audio Domain, a separate audio server environment that allows you to pull components for audio processing from Dom0.
Another change that stands out is that a new infrastructure has been implemented for maintenance, automated build, and testing of additional virtual environment templates. In addition to Gentoo, the infrastructure provides support for Arch Linux templates and Linux kernel tests.
It is also highlighted that improved build and test system, added support for checking into the GitLab CI-based continuous integration system, plus work has been done to implement support for repeatable builds of Debian-based environments, which can be used to confirm that Qubes components compile exactly from the declared sources and do not contain extraneous changes, replacement of which, for example, can be done by attacking the build infrastructure or flags in the compiler.
On the other hand, it is highlighted that added qrexec policy background process or with a new rule system for the Qrexec RPC engine that allows you to execute commands in the context of specific virtual environments. The Qrexec rule system defines who can do what and where on Qubes.
Besides, also implemented the ability to use a separate GUI domain environment with components to ensure the operation of the graphical interface. Previously, in virtual environments for each class of applications, a separate X server, a simplified window manager, and an auxiliary video driver that translated output to the control environment in composite mode were released, but the graphics stack components, the main desktop window manager, display controls, and graphics drivers all ran in the main environment.
Graphics-related functions can now be moved from Dom0 to a separate GUI domain environment and separated from system management components.
Of the other changes that stand out from this new version:
- Improved support for high pixel density displays.
- Added support for different cursor shapes.
- Implemented a notification about the lack of free disk space.
- Added support for Paranoid Backup recovery mode, which uses a one-time virtual environment for recovery.
The installer provides the option to choose between Debian and Fedora for the virtual machine templates. - Added a new graphical interface to manage updates.
- Added Template Manager utility to install, remove and update templates.
- Improved template distribution mechanism.
- The Dom0 base environment was upgraded to the Fedora 32 base package.
- The templates for generating virtual environments have been updated to Fedora 34, Debian 11, and Whonix 16.
- The default Linux kernel is 5.10. Updated Xen 4.14 hypervisor and Xfce 4.14 graphical environment.
- Rewritten firewall implementation.
- Three new virtual environment templates based on Gentoo Linux are proposed: minimal, with Xfce and with GNOME.
Si you want to know a little more about it of this new version, you can read the details in the Qubes OS 4.1 release note at following link.
Download Qubes OS
If you want to try this Qubes OS pYou can do it by downloading the system image from its official website and in its download section you will get it, you can do it in the following link
It is important to emphasize that Qubes OS can not only be installed as the main operating system, but also offers the possibility of being able to test it in its Live version.