
Although security and privacy should always be in a privileged place, from what the lack of these implies, it seems that we only remember them when a case of espionage occurs, we see news of a vulnerability or malware that affects our Linux-based systems. But it shouldn't be that way, and security should be the order of the day.
To better protect ourselves, we are going to analyze a series of security-oriented free operating systems, yes, you read that correctly, not just security-oriented Linux distributions, also other open source projects that we sometimes forget because it is a blog whose main theme is Linux, but that we should keep in mind. We could also talk about Solaris and its Trusted functionality, or other systems such as EROS or its CapROS evolution of open source, the L4 microkernel, but we will focus on other systems that are more "affordable" for most mortals, or at least better known.
Security-oriented Linux distributions
It is not about making a list of distributions aimed at making security checks or pentesting, such as Kali, Parrot, Santoku, etc., but rather to list the distributions designed so that others do not attack you, which are hardened and shielded against attacks, which ensure our security, privacy and anonymity. Although, your favorite distro you can also strengthen it if you want, and in this blog we have already given you some keys, you must also be aware that 100% security does not exist:
alpine linux:

Alpine Linux It is a distribution that, in addition to being lightweight, uses PaX and grsecurity patches in the kernel by default and compiles all packages with "stack-smashing" protection, that is, against buffer overflows that can be exploited for an attack.
Annvix:
Mandriva-based Annvix and aimed at having a secure system, with ProPolice to improve security, as well as secure settings by default, etc.
Hardened Gentoo:
Hardened Gentoo, as its name suggests, is a strengthened Gentoo distro with ProPolice, PaX, and other security systems such as intrusion detection, mandatory access control, etc.
Immunix:
Immunix is a commercial distribution hardened. Includes StackGuard, encryption, security patches, exploit protection, etc.
Time:
Mempo hides a distro Debian-based and privacy-oriented, making use of projects like Freenet or Tor.
Open Wall Project:
Open Wall Project is a distro that varies the code to have a GNU / Linux distro with a design and a strengthened Linux kernel and inspired by other projects and with a cryptography with its own modified blowfish algorithm for password hashing, and compatible with OpenBSD.
Qube's OS:
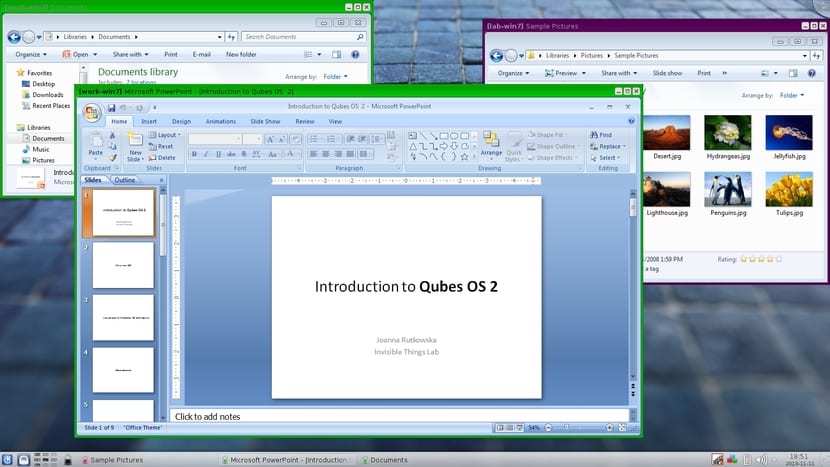
QubesOS is a distro designed to be untouchable, or so its creators say. Based on the Xen hypervisor, it can isolate programs thanks to virtual machines that prevent their problems or the dangers they imply, from affecting the security of the system itself.
replicant:

Replicant is an Android which has replaced all Android closed source with substitute open source. Therefore it is a more free version of the Google system. In addition, it has integrated certain security improvements that strengthen the base system. It can be a good option for both your mobile device and your desktop computer.
Subgraph OS:

Subgraph OS is another distro for security maniacs that do not have too high knowledge. Since from the beginning, the developers have taken care of everything to ensure our safety, facilitating the work of the end user. It emphasizes software integrity, with Grsecurity, PaX, Linux Namespaces, Xpra for containers to isolate applications, file encryption, and other strong points against attacks, in addition to Tor for the network.
Tails:

Tails or The Amnesic Incognito Live System, is another very popular distro that we have already talked about a lot. It is oriented to surf anonymously and not leave a trace on the network to respect security. Some sources say that it is the operating system used by Edward Snowden, although this information must be taken with care. We don't really know who develops it, but we do know that it is based on Debian and uses Tor and I2P for anonymity, it can also be run in Live mode so you don't even have to install it on a computer and leave a trace ...
Ubuntu Privacy Remix:
Ubuntu Privacy RemixAs its name suggests, it is an Ubuntu distro with a number of privacy tools.
Whonix:

It's another one of my favorites. Whonix is also a distro for security freaks. It is a general purpose distro that is based on Debian and uses VirtualBox to create a series of virtual machines on which applications run and the web runs on. This way it isolates the system from malware or vulnerabilities of the software we use and from the dangers of the network. A virtual machine uses Tor (optionally I2P) and acts as a gateway for the connection and is called Whonix-Gateway. The other virtual machine is known as Whonix-Workstation and it is where the applications run, totally isolated from the network.
IprediaOS:

IprediaOS is a Linux-based operating system that uses I2P for more anonymous connections. In addition, its interface is quite friendly, beautiful and simple, so you will not have too many problems with it.
Security Onions:
Security onionBy the name you can already get an idea of what it is about. It is a distribution based on Ubuntu that has a series of intrusion detection and security monitoring tools. Tools include Snort, Suricata, Sguil, Bro, and Xplico.
Other security-oriented operating systems
Worldwide presence BSD there are also good alternatives. In this blog we have never closed the door to BSD. We have always tried to give news and contributions of alternative open source operating systems such as FreeBSD, OpenBSD, etc. Well, there are also three of these BSDs that are especially important in the field of security:
OpenBSD:

OpenBSD is an operating system open source type BSD and that focuses on security as a main pillar for its development. The code is rigorously compiled by the team members, reviewing and providing security tools, such as protection for executions based on ProPolice, ASLR supported and activated by default, PIE (Position-Independent Executable) support for binaries, etc.
TrustedBSD:

TrustedBSD is a subproject of FreeBSD designed for better security. For their security they use the parameters established in the famous Orange Book, the famous security book that hackers like so much. Work with access control lists, mandatory access controls, use some other extensions for security, etc.
HardenedBSD:

HardenedBSD is a derivative or fork of FreeBSD and also geared towards enhanced security. The kernel is revised and improved to strengthen it, in addition to including other interesting tools such as ASLR, PIE, PTrace hardening, and many other functionalities to improve security. Perhaps, along with TrustedBSD, it may have similarities to Solaris security.
Tips:

My advice, do not obsess too much, just the right thing. Safety is important, but you shouldn't be obsessive about it. You can take a look at all these projects, and see the best of each one to apply it to your favorite distro. For example, if you use ElementaryOS, Ubuntu, Mint, openSuSE or any other, you can install the packages and tools that some of them have, keep it always updated, use encryption systems, or even use containers to run applications with Docker, etc.
In this blog already we have edited other articles that may interest you also and referring to safety:
- IPTABLES introduction and table types
- Squid step by step
- hardened linux
- Three tools to keep your equipment safe
- Simple firewall
- Protect yourself from malware
As for the distros, which of all should you pay special attention to? Well, I would recommend Whonix for generic use and Tails for browsing…. You can leave your comments and contributions. I hope it helps you to choose your favorite. If you want to compare some of these operating systems, you can consult this web in which Whonix is compared with other projects.
Wow.
I congratulate you for your blog and this note did not know of the existence of all these districts.
Thanks a lot. :)
You reminded me of the Tails distro which was one of the first I had tried when I started in the Linux world about 5 years ago, others like Whonix or IprediaOS (which the latter catches my attention and I'm going to try it), In case, my advice for other users regarding security, as they have said many times, is not to be so concerned when news of Linux malware appears, which despite the fact that they have appeared more in the last few months, they are not from great massiveness as in Windows, and another is to use «RkHunter» or «ChkRootKit», for the verification of BackDoors or Malware that there is and always check when installing new updates which versions of the libraries and the kernel are going to be installed, then, use calm Linux that from my work and personal experience, Linux in 5 years counted (VERY COUNTED) sometimes has brought me virus or OS problems
here we are again with the infamous linux and its trail of horrendous distros
according to here safe when neither life is the only safe thing is death delay / linux
failure / linux nonsense / linux down / linux
I only knew 2 thanks for the post :)
Linux is the best. Ignore the typical trolls