There are many alternatives to make backup copies in GNU / Linux. The truth is that the list of these types of apps is quite large, and many of them are extraordinary, but today we present you Restic, a command line tool that is characterized by making backup copies or backups quickly, safely and very efficiently. Something that is appreciated when our data and system depends on it.
We always recommend back up regularlySince in the event that we are attacked by ransomware and encryption of our documents, failure of the storage device, power outages, etc., we can lose a large amount of data irreversibly. If we have frequent backup copies, the data lost will be zero or, at least, minimal. It seems stupid and few make backup copies, but when a problem comes and we run out of them is when we truly appreciate their value ...
With Restic we have a backup program free, lightweight, open source, secure, reliable, fast and multiplatform. It is written in Go language, capable of encrypting data with AES-256 in counter mode and authentication with Poly1305-AES. Therefore we are talking about a very promising tool in terms of security. To install it we can use both git to obtain the source code and compile it from GitHub, as well as the different package managers of our favorite distro to install the restic package.
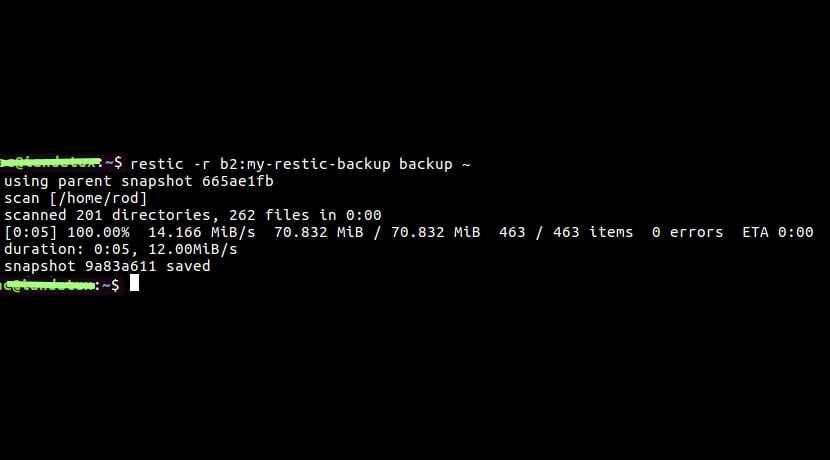
Once installed we can choose between different back ends to choose from, such as copying to a local directory, via SFTP, on an HTTP REST server, AWS S3, OpenStack Swift, BackBlaze B2, on Microsoft Azure or on Google Cloud Storage. In local format, we can make the backup like this:
restic init --repo ~/backups restic -r ~/backups backup ~/home/isaac restic -r ~/backups snapshots restic -r ~/backups restore a527cd623 --target ~/home/isaac
With the first we create a repository called backups in our Home directory, then it will ask us for a password, we make the backup with the second one in my home directory, we list the copies made to see the IDs, and with the third we can restore using the ID. The truth is that you have many options, so I advise you to see the manual, since this is just a very basic intro ...