The new version of the compact system for creating firewalls and network gateways "PfSense 2.4.5". This new version presents some improvements, but above all it comes to solve some errors that were identified in the previous version.
For those who are unaware of pfSense should know that this is a custom FreeBSD distributionwhich is adapted for use as Firewall and Router. It is characterized by being open source, it can be installed on a wide variety of computers and it also has a simple web interface for its configuration.
About pfSense
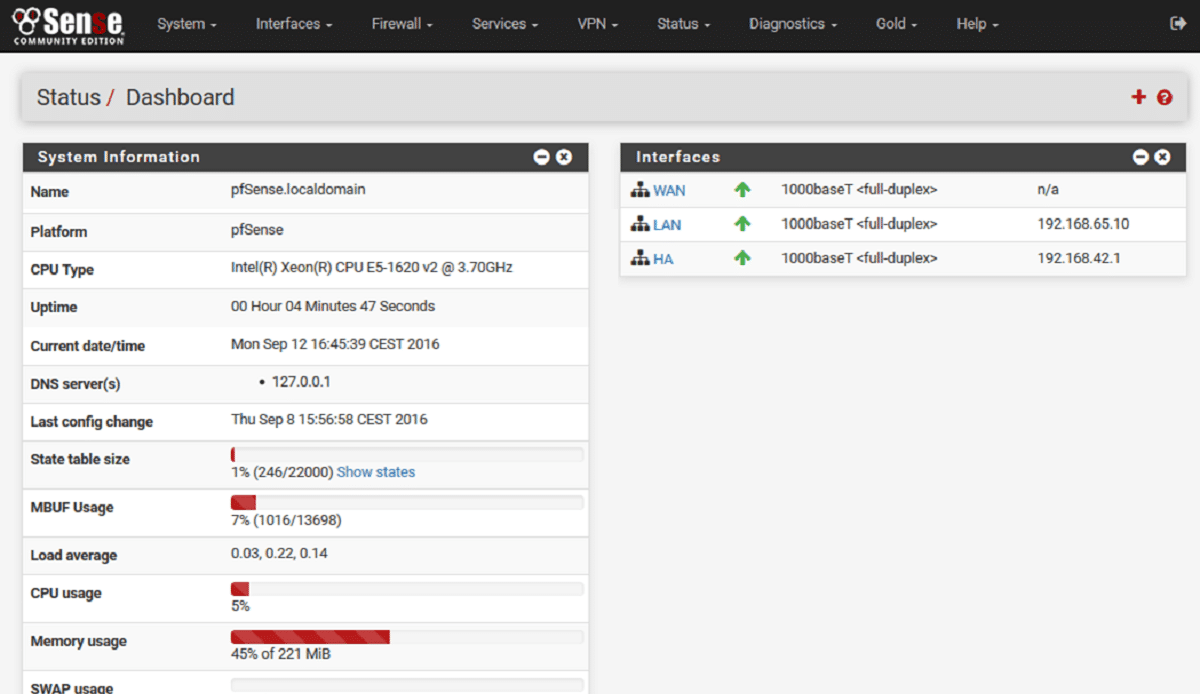
pfSense makes use of developments from the m0n0wall project and active use of pf and ALTQ. The distribution is managed through the web interface.
Captive Portal, NAT, VPN (IPsec, OpenVPN), and PPPoE can be used to organize user access on a wired and wireless network. A wide range of capabilities are supported to limit bandwidth, limit the number of simultaneous connections, filter traffic, and create CARP-based fault-tolerant configurations.
Job statistics are displayed in graphs or in table form. Authorization is supported in the local user database, as well as through RADIUS and LDAP.
Among its main characteristics it's found:
- Firewall
- State Table
- Network Address Translation (NAT)
- High availability
- Multi WAN
- Load balancing
- VPN that can be developed in IPsec, OpenVPN and in PPTP
- PPPoE server
- DNS server
- Captive portal
- DHCP server
PfSense has a package manager to expand its functionalitiesWhen choosing the desired package, the system automatically downloads and installs it. There are around seventy modules available, among which are the Squid proxy, IMSpector, Snort, ClamAV, among others.
Main new features pfSense 2.4.5
In this new issue we can find that the base system components have been updated to FreeBSD 11-STABLE.
For the part of the improvements from this new version, we can find on some pages of the web interface, including certificate manager, DHCP bind list, and ARP / NDP tables thatSupport for sorting and searching has appeared.
In the UFS file system settings for new systems, by default, the noatime mode is enabled to minimize unnecessary write operations.
On the other hand, in the unbound DNS resolver, added to Python scripting integration tools.
While for IPsec DH (Diffie-Hellman) and PFS (Perfect Forward Secrecy), Diffie-Hellman groups 25, 26, 27 and 31 were added.
In addition to this, the announcement mentions that "autocomplete = new-password" attribute has been added to authentication forms to disable auto-completion of fields with sensitive data and also added new DNS dynamic record providers: Linode and Gandi.
On the fixes side, the announcement mentions that several vulnerabilities have been fixed, including an issue in the web-based interface that allows an authenticated user with access to the image upload widget to run any PHP code and gain access to privileged pages of the administrator interface. Also, cross-site scripting (XSS) has been removed from the web-based interface.
Download and get pfSense
Finally, for those interested in being able to download and install or be able to test this system.
You can get the picture of this, from your website and in its download section you can find the links to download the system image.
In the download section we can find several images for the amd64 architecture, which vary in size from 300 to 360 MB, among them we can find a LiveCD and an image to install in USB Flash.
The image for usb can be recorded with Etcher which is a multiplatform tool. Or in the case of Windows they will be able to record the image with the help of Rufus.
While from Linux we can support ourselves from the terminal with the dd command.