Google yesterday (Thursday, June 6) I report through a publication from his Google Security Blog, which has detected the presence of a pre-installed backdoor on Android devices before leaving the factories.
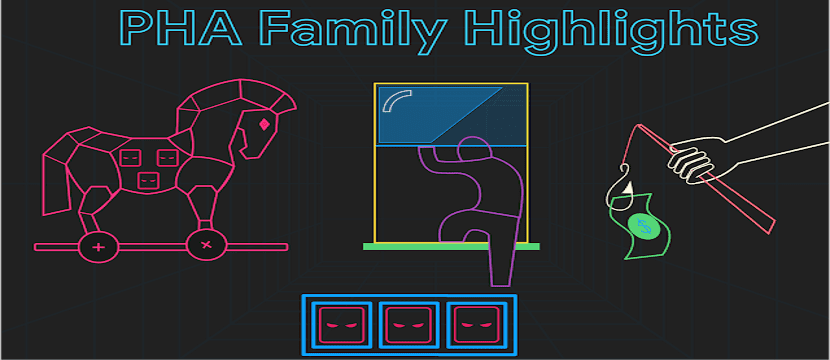
Google has studied the situation after it was revealed by computer security specialists a few years earlier. These are the malicious applications of the «Triad family» designed to spam and advertise on an Android device.
About Triada
According to Google, Triada has developed a method to install malware on Android phones virtually at the factory, even before customers started or even installed a single app on their devices.
It was in March 2016 that Triada was first described. in a blog post on the website of the computer security company Kaspersky Lab. Another blog post was dedicated by the company in June 2016.
At that moment, it was a deep-rooted Trojan unknown to analysts from the security company attempting to exploit Android devices after receiving Elevated Privileges.
As explained by Kaspersky Lab for 2016, once Triada is installed on a device, its main purpose was to install applications that could be used to send spam and display advertisements.
It used an impressive set of tools, including rooting vulnerabilities that bypass Android's built-in security protections, and ways to tweak the Android OS's Zygote process.
These are the affected brands
These malicious apps were found in 2017 pre-installed on various Android mobile devices, including smartphones from the Leagoo brand (M5 plus and M8 models) and Nomu (S10 and S20 models).
Malicious programs in this family of applications attack the system process called Zygote (the third-party application process launcher). By injecting themselves into Zygote, these malicious programs can infiltrate any other process.
"Libandroid_runtime.so is used by all Android applications, so the malware injects itself into the memory area of all running applications as the main function of this malware is to download additional malicious components. «
Because it was built in one of the system libraries operational and is located in the System section, which cannot be removed using standard methods, according to the report. Attackers have been able to quietly use the back door to download and install rogue modules.
According to the report on the Google Security Blog, Triada's first action was to install a superuser type of binary files (su).
This subroutine allowed other applications on the device to use root permissions. According to Google, the binary used by Triada required a password, which means that it was unique compared to binaries common to other Linux systems. This meant that the malware could directly spoof all installed applications.
According to Kaspersky Lab, they explain why Triada is so difficult to detect. First, modifies the Zygote process. Zygote It is the basic process of the Android operating system that is used as a template for each application, which means that once the Trojan enters the process, it becomes part of every application which starts on the device.
Second, it overrides the system functions and hides its modules from the list of running processes and installed applications. Therefore, the system does not see any strange processes running and therefore does not throw any alerts.
According to Google's analysis in their report, other reasons have made the Triada family of malicious apps so sophisticated.
On the one hand, it used XOR encoding and ZIP files to encrypt communications. On the other hand, she injected code into the system's user interface application that allowed to display ads. The backdoor also injected code into him that allowed him to use the Google Play app to download and install apps of his choice.