Firejail is a SUID program that reduces the risk of security breaches by restricting the application execution environment
Announced the launch of the new version of the Firejail project 0.9.72, which develops a system for the isolated execution of graphic applications, console and server, which allows you to minimize the risk of compromising the main system by running untrusted or potentially vulnerable programs.
For isolation, Firejail use namespaces, AppArmor and system call filtering (seccomp-bpf) on Linux. Once started, the program and all of its child processes use separate representations of kernel resources, such as the network stack, process table, and mount points.
Applications that depend on each other can be combined into a common sandbox. If desired, Firejail can also be used to run Docker, LXC, and OpenVZ containers.
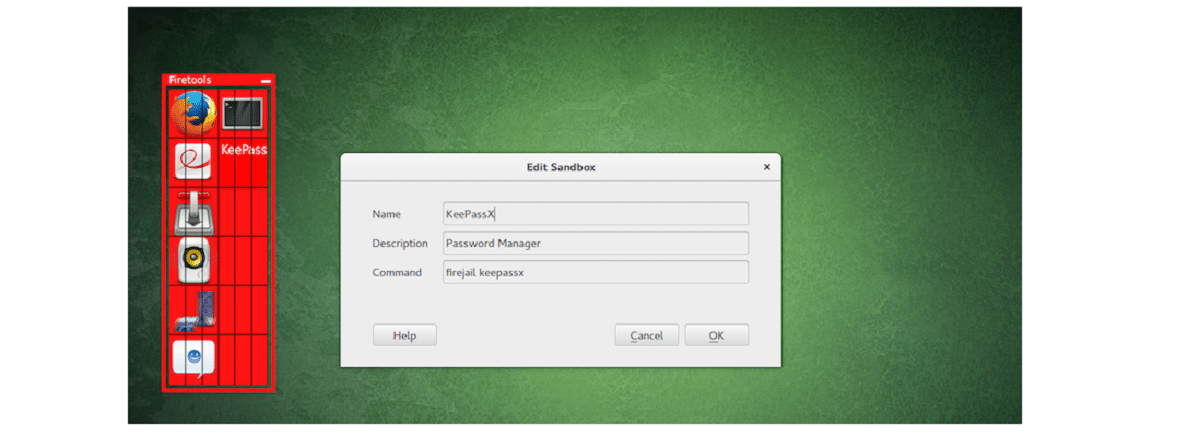
A lot of popular apps, including Firefox, Chromium, VLC, and Transmission, have pre-configured system call isolation profiles. To gain the necessary privileges to set up a sandboxed environment, the firejail executable is installed with the SUID root prompt (privileges are reset after initialization). To run a program in isolated mode, simply specify the application name as an argument to the firejail utility, for example, "firejail firefox" or "sudo firejail /etc/init.d/nginx start".
Main news of Firejail 0.9.72
In this new version we can find that added seccomp system call filter to block namespace creations (added “–restrict-namespaces” option to enable). Updated system call tables and seccomp groups.
mode has been improved force-nonewprivs (NO_NEW_PRIVS) It improves security guarantees and is intended to prevent new processes from gaining additional privileges.
Another change that stands out is that the ability to use your own AppArmor profiles was added (the option “–apparmor” is suggested for the connection).
We can also find that the nettrace network traffic monitoring system, which displays information about the IP and traffic intensity of each address, supports ICMP and provides the options “–dnstrace”, “–icmptrace”, and “–snitrace”.
Of the other changes that stand out:
- Removed the –cgroup and –shell commands (default is –shell=none).
- Firetunnel build stops by default.
- Disabled chroot, private-lib and tracelog configuration in /etc/firejail/firejail.config.
- Removed support for grsecurity.
- modif: removed the –cgroup command
- modif: set --shell=none as default
- modify: removed --shell
- modif: Firetunnel disabled by default in configure.ac
- modif: removed grsecurity support
- modif: stop hiding blacklisted files in /etc by default
- old behavior (disabled by default)
- bug fix: flooding seccomp audit log entries
- bugfix: --netlock not working (Error: no valid sandbox)
Finally, for those who are interested in the program, they should know that it is written in C, is distributed under the GPLv2 license, and can run on any Linux distribution. Firejail Ready packages are prepared in deb formats (Debian, Ubuntu).
How to install Firejail on Linux?
For those interested in being able to install Firejail on their Linux distribution, they can do it following the instructions that we share below.
On Debian, Ubuntu and derivatives the installation is quite simple, since they can install Firejail from the repositories of its distribution or they can download the prepared deb packages from the following link.
In the case of choosing the installation from the repositories, just open a terminal and execute the following command:
sudo apt-get install firejail
Or if they decided to download the deb packages, they can install with their preferred package manager or from the terminal with the command:
sudo dpkg -i firejail_0.9.72-apparmor_1_amd64.deb
While for the case of Arch Linux and derivatives from this, just run:
sudo pacman -S firejail
Configuration
Once the installation is done, now we will have to configure the sandbox and we also have to have AppArmor enabled.
From a terminal we are going to type:
sudo firecfg sudo apparmor_parser -r /etc/apparmor.d/firejail-default
To know its use and integration you can consult its guide In the following link.