Last year, Nick Nguyen, Vice President of Products at Mozilla, lamented that "atSome trackers send users to the fingerprinting socket”, A technique that allows the hidden identification of users through the information provided by the devices and that users are unable to control.
Plus other sites implement scripts that silently mine crypto currencies on the user's device. Believing that "such practices make the Web a more hostile place," he assured that "future versions of Firefox will block these practices by default."
Last month, Informed sources suggested that Mozilla plans to integrate the next version of its anti-fingerprinting technology in the web browser that protects against certain fingerprinting methods in relation to the size of the window, called «letterboxing».
Be supposed to this feature takes time to fill the resized web browser window with the actual content of the page Long enough for the ad code to read the wrong window dimensions.
Fingerprinting and unauthorized mining are not welcomed
The general idea is that "Letterboxing" will hide the actual dimensions of the window keeping the width and height of the window in multiples of 200px and 100px during the resize operation, generating the same window dimensions for all users and then adding a “gray space” at the top, bottom, left or right of the current page.
Letterboxing is not a new technique. Mozilla is integrating a feature that was originally developed for the Tor browser four years ago, in January 2015.
Y is that this type of abuse by various websites achieved a boom for several months in previous years, such is the famous case of The Pirate Bay in which it implemented a script on its website to use the resources of its visitors' computers to perform cryptocurrency mining.
And it is that nobody had noticed it, there was only something in common, that when they visited the site their computer began to slow down and that it used a lot of resources. It wasn't until a user decided to check out the site's source code and discovered the script.
With that this was a boom so many people ill-intentioned they will launch extensions or inject them with code for the cryptocurrency miner.
Another very popular case was that of the utorrent client which did the same, use the computer of its users for cryptocurrency mining.
Finally, we can say that Firefox is not the first browser to implement this type of protection since the pioneer of blocking mining by websites is Opera.
Firefox against bad practices and the good of its users
Mozilla announced recently on your site the release of Firefox 68 (Nightly Edition) and Firefox Beta 67, incorporating an experimental feature that allows users to better protect themselves against fingerprinting and cryptojacking (referring to techniques that allow the browser to secretly use the resources of a device other than its own to mine cryptocurrencies).
As part of the development of these new protection tools in collaboration with Disconnect, the Firefox publisher specified to have compiled lists of various domains involved in spreading malicious target scripts.
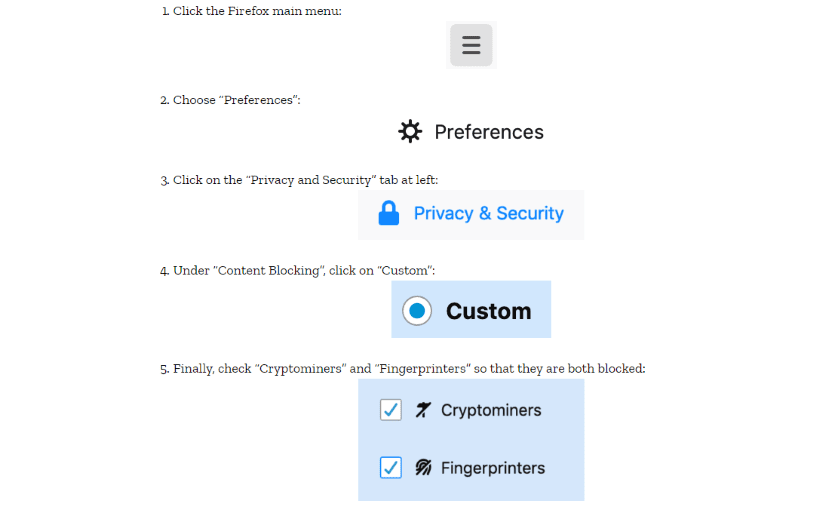
The feature is not enabled by default. Firefox users will need to go to: Main menu - Options - Privacy and security - Content blocking.
Then they will have to select the "custom" mode to block the content and finally activate the fingerprinting detection and anti-cryptojacking functions of the browser.
Mozilla has also said:
“In the coming months, we will begin to test these protections with small groups of users and continue to work with Disconnect to improve and expand all areas blocked by Firefox. We plan to enable these default protections for all Firefox users in a future release.