Recently Microsoft released the first stable version of its own distribution Linux "CBL-Mariner 1.0" (Common Base Linux) which is a Microsoft product that is used internally for the cloud and other business needs of the company.
As such CBL-Mariner not a general purpose distribution like any other we would have in mind (such as Ubuntu or Fedora) although it is open source y is already being used by systems like Windows Subsystem for Linux (WSL), Azure Sphere OS, SONiC and other Linux-based efforts.
Esto is what Juan Manuel Rey, member of the Azure team, shares on his blog, as it specifies that this distribution called CBL-Mariner is intended for internal use to develop products and services in the cloud.
In your post, you specify:
CBL-Mariner follows the principle of security by default, most aspects of the operating system have been created with an emphasis on security. It comes with a hardened kernel, signed updates, ASLR, compiler-based hardening, and tamper-proof registries, among many features.
The project aims to unify the Linux solutions used in Microsoft and simplify the maintenance of Linux systems for various purposes to date. All software technologies in this practice are released under the MIT license.
The distribution is remarkable, since pProvides a typical small set of basic packages that act as a universal base for creating container fill, host environments and services running on cloud infrastructures and edge devices. More complex and specialized solutions can be created by adding additional packages on top of CBL-Mariner, but the foundation for all of these systems remains unchanged, simplifying maintenance and preparing for upgrades.
CBL-Mariner build system allows to generate separate RPM packages based on SPEC files and source codes, and monolithic system images generated using the rpm-ostree toolkit and atomically updated without breaking into separate packages, plus also more complex and specialized solutions can be created by adding additional fuel in SVL-Mariner, but the basis for all these times
Two upgrade models are supported: updating only individual packages and running and updating the entire system image.
To use the "maximum security by default" approach. It is possible to filter system calls with the help of the sensor mechanism, encrypt sections of the disk, verify passwords by their digital signature and much more.
By default, the protection mechanisms against wall overflow, buffer overflow, and page vulnerability of format. The address space randomization modes supported by the Linux kernel are enabled, as well as various protection mechanisms against attacks associated with symbolic links, mmap, / dеv / mem, and / dеv / kmеm.
How to install Microsoft CBL-Mariner?
For those who are interested in learning more about CBL-Mariner, they should know that they can build their own image from Ubuntu or any Linux distribution, only in this case we will take the instructions to generate the image in Ubuntu.
To do this first, we must urge some prerequisites that we will need to build the ISO image:
sudo apt install make tar wget curl rpm qemu-utils golang-go genisoimage python2-minimal bison gawk
Now we proceed to obtain the code from CBL-Mariner:
git clone https://github.com/microsoft/CBL-Mariner.git
And now we will have to enter the CBL-Mariner / toolkit directory and create the installation ISO image.
cd CBL-Mariner/toolkit sudo make iso REBUILD_TOOLS=y REBUILD_PACKAGES=n CONFIG_FILE=./imageconfigs/full.json
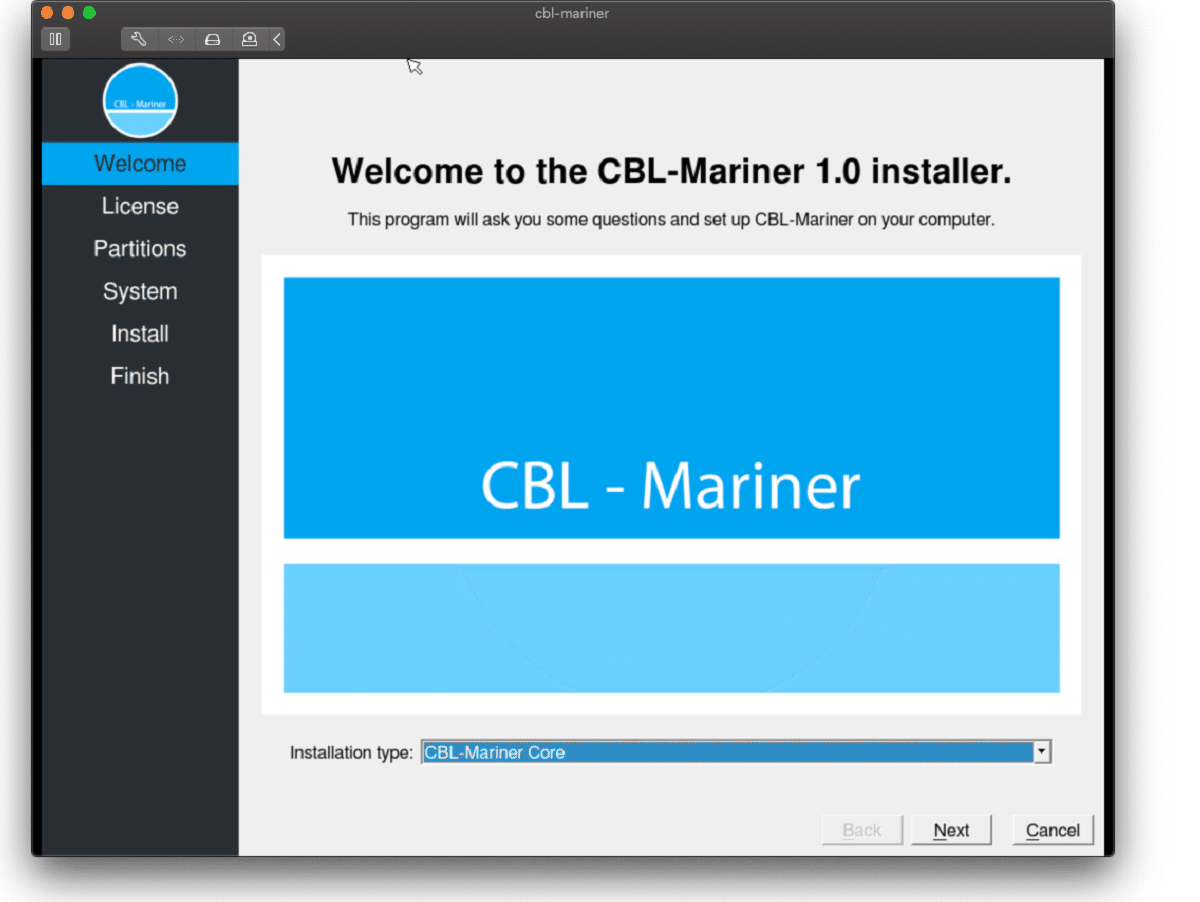
At the end, we can find the ISO file in the directory ../out/images/full/. With the system image created, we can test the system on a virtual machine, either with VirtualBox, VMWare, Boxes or any other of your liking.
The only thing you have to configure in the virtual machine is that it has at least 2GB of RAM, a core and 16GB of storage.
Finally if you are interested in knowing more about it, you can check the details In the following link.