
For whom it is use Linux in various fields (servers or desktops), know that for each task there can be multiple possible solutions. A very good example of that is in the field of backups.
There are a number of options to choose from when attempting to back up. of your data, even when you are looking to back up your data over a network. One such solution is the open source BorgBackup. This a deduplication backup program that supports compression and authenticated encryption.
Data deduplication is a technique to eliminate duplicate copies of repeating data. A related and somewhat synonymous term is single instance storage.
About BorgBackup
The main objective by BorgBackup is to provide an efficient and secure way to back up data.
The data deduplication technique used makes BorgBackup suitable for daily backups as only changes are stored.
The authenticated encryption technique makes it suitable for backups to destinations that are not completely trusted.
BorgBackup can store data on any remote host accessible via SSH. If Borg is installed on the remote host, huge performance gains can be achieved compared to using a network file system (sshfs, nfs, etc).
Backups can be mounted as file systems. Backup files can be mounted as user-space file systems for easy interactive browsing of backups and restores (for example, using a regular file manager).
All data can be protected by 256-bit AES encryption, data integrity and authenticity are verified using HMAC-SHA256. The data is encrypted on the client side.
In addition to that, all data can be compressed with lz4 (super fast, low compression), zlib (medium speed and compression) or lzma (low speed, high compression).
The main features include:
- Content-defined chunk-based deduplication is used to reduce the number of bytes stored: each file is split into multiple chunks of varying length, and only chunks that have never been seen before are added to the repository.
- Speed: Performance critical code (fragmentation, compression, encryption) is implemented in C / Cython
- Local file and data cache
- Fast detection of unmodified files.
- Data encryption
How to install BorgBackup on Linux?
For those who are interested in being able to install this tool on their systems, You can do so by following the instructions we share with you below.
If they are Debian, Ubuntu, Linux Mint users or any other derivative of these, we are going to install the Borg from the terminal by executing the following command:
sudo apt install borgbackup
While for Arch Linux, Manjaro, Antergos or any other derivative of Arch Linux, They must have the community repository enabled in their pacman.conf file.
The command to install it is:
sudo pacman -S borg
Users of Fedora, CentOS, RHEL or any other derivative of these, install it with:
sudo dnf install borgbackup
For the case of those who are Users of any version of OpenSUSE, can install with the following command:
sudo zypper in borgbackup
Finally, for those who are Gentoo users, install Borg con:
emerge borgbackup
Installing a graphical interface (GUI) for Borg
Natively Borg is managed from the command line, so if you intend to use this tool on a desktop computer (that is, you manage a desktop environment) the most convenient thing is that you manage Borg from a graphical interface.
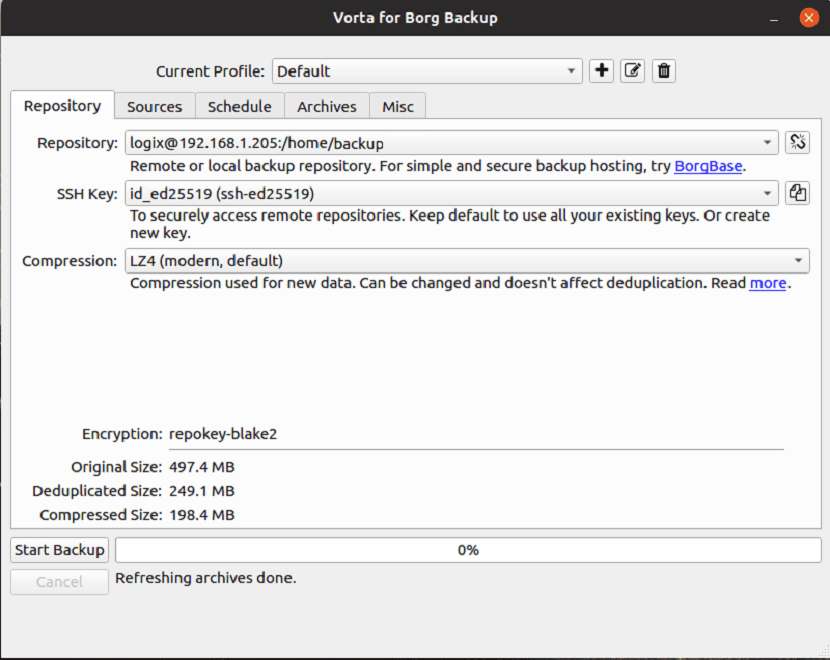
For this we are going to install Vorta (Borg's graceful interface). We can install this in our system in a generic way as a Python package using PIP.
In a terminal we are going to type the following:
pip3 install vorta
And that's it, we can start using Borg.
Si Do you want to know a little more about Borg? and its form of use from the terminal you can visit the following link.