There is no doubt that information security on the network is paramount, more and more we are getting to know cases where Hackers manage to create a new method to breach security measures implemented in various computer systems.
Since the famous case in which the Movistar company suffered an attack, cases of the same type have been raised, but with variants of the attack. If one thing I strongly agree on is that it doesn't matter how secure a system is, If the human factor is involved, it is the gap to enter.
And why do I say this, it is simple, many of the attackers take advantage of human error to obtain the information they want And it is that from a simple exploit, if the victim does not have the slightest idea of how to differentiate between a real site and a fake, he is simply lost.
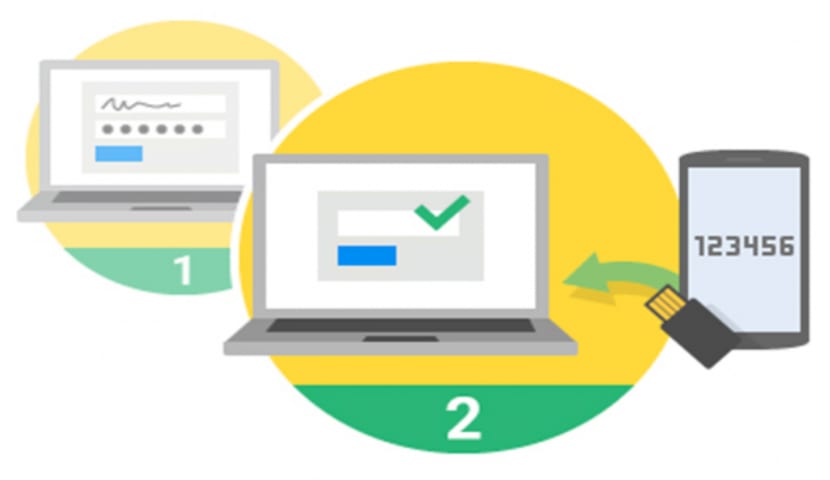
A very simple way to protect your information, even if you fall into fake sites, is using two-step authentication.
This method It works in the following way: to enter a site you require a username and password, this information in theory is only yours.
But what happens when you enter it on a fake site or someone else manages to obtain that data?
This is when two-step authentication comes in, andThis is an extra security measure, which works in a similar way to the tokens that are provided to you in banks.
You receive a code, usually 6 digits, either to your email, by sms, phone call or with an application that is linked to your cell phone.
This code must be entered and is only generic, since it has an expiration time if you will not have to generate a new one.
As a personal comment, this measure is good, since it not only protects your information, since, if you use your smartphone to receive the codes, you receive the alert that someone else is trying to access your information and that is when you are in time to change your credentials.
How to implement a two-step verification in Linux?
Personally, I did not know of any service or software that I could implement in my system, that was until recently.
Surfing the net I came across Authenticator, this software is responsible for generating codes for it.
Authenticator is an application developed to work in environments like GnomeAlthough it works well over others as well, Authenticator is easy to use.
Authenticator is compatible with more than 250 services, including the most popular among them we find:
Facebook, Google, Twitter, Apple, Amazon, Evernote, Gmail, YouTube, Twitch, Dropbox, ProtonMail, LastPass, OneDrive, Reddit among many others.
How to install Authenticator on Linux?

In order to start using this tool on our system, we can obtain it in a fairly simple way, we only have to have the support to be able to install flatpak applications in our distribution.
If we count it, we just have to open a terminal and use the following command to install the program through Flatpak.
flatpak remote-add --if-not-exists flathub https://dl.flathub.org/repo/flathub.flatpakrepo flatpak install flathub com.github.bilelmoussaoui.Authenticator
Be patient, as many times it can take several minutes for Flatpak to download everything it needs. We may be asked to install the GNOME Runtime.
Ready with it, you already have Authenticator installed on your system. Now when you want to start the program, enter in a terminal.
flatpak run com.github.bilelmoussaoui.Authenticator
For update the program to a new version, if it is available we just have to execute the following command:
flatpak --user update com.github.bilelmoussaoui.Authenticator
Now if, on the contrary, what you want to do is uninstall the application, on a terminal you must execute the following command:
flatpak --user uninstall com.github.bilelmoussaoui.Authenticator
Finally, I will test the service for a while. I have read on the net that there are other programs, but as I personally comment, I was unaware of them.
If you know or use a service other than Authenticator, do not hesitate to share it in the comments.